Comptia Security+ SY0-601 Exam: A Comprehensive Study Plan
Embarking on your SY0-601 journey requires dedication; mastering concepts through practice is key to confidently tackling the certification challenge ahead.
The CompTIA Security+ SY0-601 exam is a globally recognized validation of foundational cybersecurity skills. It’s designed for IT professionals with approximately one to three years of hands-on security experience, demonstrating competency in essential principles and practices. Passing this exam signifies your ability to assess the security posture of an organization, identify and address vulnerabilities, and respond effectively to security incidents.
This certification isn’t merely about memorizing facts; it’s about understanding why security measures are implemented. The SY0-601 covers a broad spectrum of topics, from network security and cryptography to risk management and compliance. Preparing effectively requires a holistic approach, combining theoretical knowledge with practical application. Success on this exam opens doors to numerous career opportunities in the cybersecurity field, establishing a solid base for further specialization.
Understanding the Exam Objectives
The SY0-601 exam objectives are your roadmap to success, outlining the specific knowledge and skills CompTIA expects you to demonstrate. These objectives are categorized into five domains: Threats, Attacks, and Vulnerabilities (24%); Architecture and Design (21%); Implementation (25%); Operations and Incident Response (16%); and Governance, Risk, and Compliance (14%).
Each domain contains numerous sub-objectives detailing the precise topics covered. Thoroughly reviewing these objectives is crucial for focusing your study efforts. Don’t simply skim them; break down each sub-objective and ensure you understand the underlying concepts. Prioritize areas where your knowledge is weakest. Utilizing resources aligned with these objectives – study guides, practice exams, and video courses – will maximize your preparation and increase your chances of passing the exam on your first attempt.
Threats, Attacks, and Vulnerabilities (24%)
This domain focuses on identifying and analyzing various security threats, understanding common attack vectors, and recognizing vulnerabilities within systems and applications. Key areas include malware types (viruses, worms, Trojans, ransomware), social engineering tactics (phishing, vishing, pretexting), and network-based attacks (DoS, DDoS, man-in-the-middle).
You’ll need to understand vulnerability scanning and penetration testing methodologies, as well as common vulnerabilities like buffer overflows, SQL injection, and cross-site scripting (XSS). Familiarize yourself with threat intelligence sources and the MITRE ATT&CK framework. Be prepared to differentiate between various attack phases and the impact of successful exploits. A strong grasp of these concepts is vital for protecting systems and data against evolving threats, representing a significant portion of the SY0-601 exam.
Architecture and Design (21%)
This section assesses your understanding of secure system design principles and the implementation of security controls within various architectures. Expect questions on cloud computing concepts (IaaS, PaaS, SaaS) and their associated security considerations. You’ll need to know about secure network architecture, including segmentation, VLANs, and VPNs.
Focus on understanding the principles of least privilege, defense in depth, and zero trust. Be prepared to analyze different security architectures and identify potential weaknesses. Knowledge of virtualization technologies and containerization is also crucial. The exam will test your ability to apply security best practices to system design, ensuring confidentiality, integrity, and availability. Understanding secure protocols and their proper implementation is paramount for success in this domain.
Implementation (25%)
This domain focuses on the practical application of security controls and technologies. Expect a significant portion of questions relating to identity and access management (IAM), including authentication methods like MFA and password policies. You’ll need to demonstrate knowledge of implementing secure configurations for operating systems, network devices, and applications.
Wireless security protocols (WPA2/3) and secure remote access solutions are key areas. Be prepared to analyze scenarios involving vulnerability remediation and patching. Understanding the implementation of security tools like firewalls, intrusion detection/prevention systems (IDS/IPS), and endpoint detection and response (EDR) is vital. The exam will test your ability to configure and deploy security solutions effectively, ensuring a robust security posture. Practical knowledge is heavily emphasized here.

Operations and Incident Response (16%)
This section assesses your understanding of maintaining a secure environment and responding to security incidents. Expect questions covering security monitoring and logging, focusing on identifying anomalies and potential threats. You’ll need to demonstrate knowledge of the incident response lifecycle – preparation, identification, containment, eradication, recovery, and lessons learned.
Forensic investigation basics, including evidence collection and chain of custody, are crucial. Understanding different types of malware and attack vectors is essential for effective incident handling. Be prepared to analyze scenarios involving data breaches and system compromises. The exam will test your ability to prioritize responses based on impact and severity, and to effectively communicate incident details to stakeholders. Proactive monitoring and swift response are key.

Governance, Risk, and Compliance (14%)
This domain focuses on the policies, procedures, and regulations governing information security. You’ll be tested on understanding risk management processes – identifying, assessing, and mitigating risks to organizational assets. Familiarize yourself with common compliance frameworks like NIST, ISO 27001/27002, and GDPR.
Expect questions regarding data privacy laws and regulations, as well as the importance of security awareness training for employees. Understanding the roles and responsibilities within a security governance structure is vital. The exam will assess your ability to apply security controls to meet specific compliance requirements. Be prepared to analyze scenarios involving legal and ethical considerations related to data security and privacy. Policy enforcement and regular audits are key components.
Essential Resources for Preparation
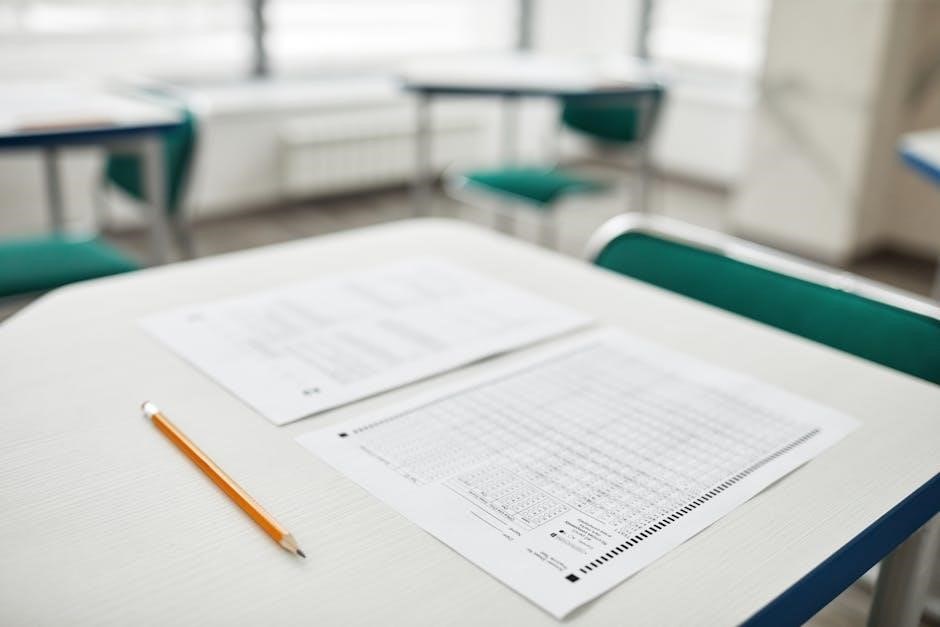
Success with the SY0-601 demands a diverse study approach. While practice questions are valuable, relying solely on question dumps is detrimental to genuine understanding. The Official CompTIA Study Guide provides a foundational understanding of all exam objectives. Supplement this with robust practice exams from providers like Dion Training and MeasureUp to gauge your readiness.
Professor Messer’s free video series offers a comprehensive overview, while Mike Meyers provides a more engaging, hands-on learning experience. Remember to actively engage with the material – take notes, create flashcards, and practice applying concepts. Focus on understanding why answers are correct, not just memorizing them. Utilize online forums and study groups for collaborative learning and support.

Official CompTIA Study Guide
The Official CompTIA Study Guide is the cornerstone of your SY0-601 preparation. It directly aligns with the exam objectives, providing a thorough exploration of each domain. This resource isn’t merely a collection of facts; it’s designed to build a solid conceptual foundation. Expect detailed explanations, real-world scenarios, and review questions at the end of each chapter.
However, don’t treat it as your only resource. Supplement the guide with practice exams and video courses to reinforce your learning. Actively work through the review questions, and don’t shy away from areas where you struggle. The guide’s strength lies in its comprehensive coverage, making it an invaluable asset for understanding the breadth of the SY0-601 exam content.
Practice Exams (Dion Training, Jason Dion, MeasureUp)
Simulating the exam environment is crucial, and practice exams are your best tool. Dion Training and Jason Dion offer highly-regarded exam simulations known for their challenging questions and detailed explanations. MeasureUp provides another excellent option, often mirroring the exam’s difficulty and format closely.
Don’t just take the exams; analyze your results. Identify weak areas and revisit the corresponding topics in the official study guide or video courses. Focus on understanding why you missed a question, not just memorizing the correct answer. Aim for consistent scores of 80% or higher before attempting the real exam. These practice tests build confidence and refine your test-taking strategy.
Video Courses (Professor Messer, Mike Meyers)
Visual and auditory learners will benefit greatly from comprehensive video courses. Professor Messer’s course is a staple for many SY0-601 candidates, offering concise, focused lessons covering every exam objective – and it’s completely free! Mike Meyers delivers a more engaging, story-driven approach, making complex topics more accessible.
Supplement your reading with these dynamic resources. Watch the videos alongside the official study guide, pausing to take notes and complete practice questions. Utilize the course notes provided by both instructors. Regularly revisiting key concepts through video reinforces learning and improves retention. Combine both instructors’ styles for a well-rounded understanding of the material.
Core Security Concepts
A solid grasp of fundamental security principles is paramount for success on the SY0-601 exam. The CIA Triad – Confidentiality, Integrity, and Availability – forms the bedrock of information security. Understand how these principles apply to various security controls and scenarios.
Risk Management is also crucial; learn to identify, assess, and mitigate vulnerabilities. Familiarize yourself with concepts like risk appetite, threat modeling, and vulnerability scanning. Network Security basics, including the TCP/IP model, common ports, and network segmentation, are heavily tested. Mastering these core concepts will provide a strong foundation for tackling more advanced topics throughout your studies.
Confidentiality, Integrity, and Availability (CIA Triad)
The CIA Triad is the cornerstone of information security, and the SY0-601 exam heavily emphasizes its understanding. Confidentiality ensures data is accessible only to authorized individuals, often achieved through encryption and access controls. Integrity guarantees data accuracy and completeness, protected by hashing and version control.

Availability ensures timely and reliable access to information, maintained through redundancy and disaster recovery planning. Exam questions frequently present scenarios requiring you to identify which element of the triad is compromised or how to best protect each. Recognizing controls that support each principle – like MFA for confidentiality – is vital for success.
Risk Management Fundamentals
A core component of the SY0-601 exam is understanding risk management processes. This begins with identification – pinpointing potential threats and vulnerabilities. Next is assessment, evaluating the likelihood and impact of those risks. Following assessment, risk response strategies are crucial: accept, transfer, mitigate, or avoid.
Monitoring and reporting are ongoing processes to ensure effectiveness. Expect questions involving calculating Annualized Loss Expectancy (ALE) and determining appropriate controls based on risk levels. Familiarize yourself with qualitative versus quantitative risk analysis. The exam tests your ability to apply these fundamentals to real-world scenarios, prioritizing security investments based on potential business impact.
Network Security Essentials
The SY0-601 exam heavily emphasizes network security concepts. Understanding network topologies, protocols, and common attacks is vital. Focus on securing network devices like routers and switches, and implementing access control lists (ACLs). Network segmentation, using VLANs and firewalls, is a key defense strategy.
Expect questions regarding wireless security protocols (WPA2/3) and the importance of secure remote access (VPNs); Knowledge of intrusion detection and prevention systems (IDS/IPS) is also crucial. Be prepared to analyze network traffic for malicious activity. The exam will assess your ability to apply security best practices to protect network infrastructure and data transmission.
TCP/IP Model and Common Ports
A solid grasp of the TCP/IP model is fundamental for the SY0-601 exam. Understand each layer’s function – Application, Transport, Network, and Data Link – and how data encapsulation occurs. Common ports and their associated services are frequently tested; know the standard ports for HTTP(S), SSH, DNS, SMTP, and others.
Be prepared to identify vulnerabilities associated with specific ports and protocols. Questions may involve troubleshooting network connectivity issues and recognizing attacks targeting specific services. Familiarize yourself with port scanning techniques and how to mitigate them. Understanding the difference between TCP and UDP, and their respective uses, is also essential for exam success.
Network Segmentation and Firewalls
Network segmentation is a crucial security practice, and the SY0-601 exam will test your understanding of its benefits. Learn how dividing a network into smaller, isolated segments limits the blast radius of security incidents; Firewalls are central to this concept; understand their different types – packet filtering, stateful inspection, and next-generation firewalls (NGFWs).
Be prepared to analyze firewall rule sets and identify potential vulnerabilities. Questions may involve determining the appropriate firewall configuration to allow or deny specific traffic. Understand DMZs, VLANs, and microsegmentation. Know how firewalls interact with other security devices and the importance of regular firewall log analysis for threat detection and incident response.
Cryptography and Access Control
Cryptography is fundamental to data security, and the SY0-601 exam heavily emphasizes it. You’ll need to differentiate between symmetric and asymmetric encryption, understanding the strengths and weaknesses of each. Focus on common algorithms like AES, RSA, and hashing functions like SHA-256. Be prepared to explain how these algorithms protect data confidentiality, integrity, and authenticity.
Access control is equally vital. Understand the principles of least privilege and need-to-know. The exam will cover various access control models – DAC, MAC, and RBAC. Know the differences between authentication, authorization, and accounting (AAA). Familiarize yourself with multi-factor authentication (MFA) and biometric methods. Expect questions on certificate authorities and digital signatures.
Encryption Algorithms (AES, RSA)
Advanced Encryption Standard (AES) is a symmetric-key algorithm, widely used for its speed and security. Understand its key sizes (128, 192, and 256 bits) and how they impact strength. RSA, a cornerstone of public-key cryptography, relies on the mathematical complexity of factoring large numbers. Know its use in key exchange and digital signatures.

The SY0-601 exam requires you to differentiate between these algorithms. Understand how they’re applied in various scenarios – securing data at rest, data in transit, and establishing secure communications. Be prepared to explain the concepts of key management and the importance of strong key generation. Focus on practical applications and potential vulnerabilities associated with each algorithm.

Authentication Methods (MFA, Biometrics)
Multi-Factor Authentication (MFA) significantly enhances security by requiring multiple verification factors – something you know, something you have, or something you are. Understand the different MFA methods like SMS codes, authenticator apps, and hardware tokens. Biometrics utilize unique biological traits for identification, including fingerprint scanning, facial recognition, and iris scans.
The SY0-601 exam will test your knowledge of the strengths and weaknesses of each method. Be prepared to discuss the trade-offs between security and usability. Know how these methods mitigate risks associated with password-based authentication. Focus on practical implementation and common attack vectors targeting authentication systems. Understand the importance of secure storage and handling of biometric data.
Incident Response and Forensics
Incident Response is a structured approach to handling security breaches, minimizing damage, and restoring operations. The Incident Response Lifecycle – Preparation, Identification, Containment, Eradication, Recovery, and Lessons Learned – is crucial. You must understand each phase and associated actions. Digital Forensics focuses on collecting, preserving, and analyzing digital evidence.
The SY0-601 exam expects you to know basic forensic techniques like imaging hard drives, analyzing logs, and identifying malware. Understand the importance of maintaining the chain of custody. Be prepared to differentiate between various types of malware and their impact. Know how to properly document findings and report incidents. Focus on the legal and ethical considerations surrounding digital forensics investigations.
Incident Response Lifecycle
The Incident Response Lifecycle is a six-stage process for effectively managing security incidents. Preparation involves establishing policies, training staff, and securing necessary tools. Identification focuses on detecting and verifying security events. Containment limits the scope and impact of the incident – segmentation is key here.
Eradication removes the root cause of the incident, while Recovery restores affected systems and data. Finally, Lessons Learned involves documenting the incident and improving future responses. Understanding the order and actions within each stage is vital. The SY0-601 exam will test your ability to apply this lifecycle to various scenarios, emphasizing proactive planning and efficient execution.
Basic Forensic Investigation Techniques
Digital forensics involves collecting, preserving, and analyzing digital evidence. Imaging a drive creates a bit-by-bit copy, ensuring the original remains untouched. Hashing (MD5, SHA256) verifies data integrity – any alteration changes the hash value. Chain of custody meticulously documents evidence handling, maintaining its admissibility.
Timeline analysis reconstructs events by examining timestamps from logs and files. File carving recovers deleted files based on file headers and footers. Memory analysis examines RAM for running processes and malicious code. The SY0-601 exam expects familiarity with these techniques, emphasizing proper procedures to avoid evidence contamination and maintain legal defensibility. Knowing the purpose of each step is crucial.